ZoneAlarm Anti-Ransomware
Protect your PC with the most advanced technology to keep hackers away from your data.
- Award-winning ransomware prevention
- Simple to use, compatible with all antiviruses
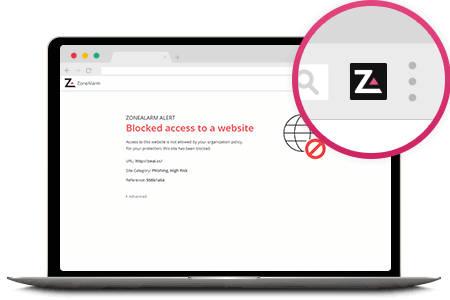
- Real-time phishing protection for online shopping & banking
- File-scanning in the Cloud safeguards your files from hidden threats
- 30-day money-back guarantee
- 24/7 online help